What is IBM i End to End Monitoring and Security?
Without a framework to help ensure that you are managing risk, assuring system availability, and being able to react to changing security conditions such as hacks and malware infections, you may put your critical data at risk. One security breach can put your whole business at risk. Increased regulations also require organizations to know who is accessing your systems, how they are accessing them and what they are doing once access is granted.
To secure, audit, and monitor your IBM i systems, SEA software offers a complete IBM i end to end monitoring and security framework, which includes a free security assessment and a complete line of software for meeting your security and compliance objectives.
Let’s look at our end to end monitoring and security framework and show how it can help you meet your security and compliance goals.
SEA’s IBM i end to end monitoring and security framework
A good IBM i end to end monitoring and security framework allows organizations to ensure that their systems are secure and available while meeting audit requirements. Effective monitoring and security encompasses these three critical activities in the framework listed in figure 1.
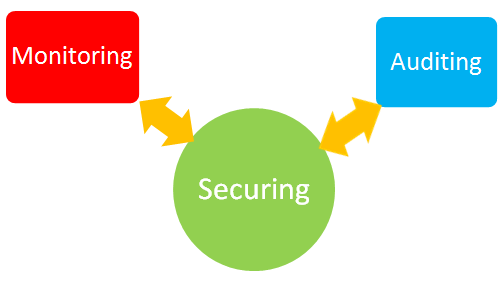
Figure 1: The three critical activities of an end to end monitoring & security framework for the IBM i
- Securing your IBM i.The IBM i is a highly securable system… but it doesn’t come that way. It’s up to you to secure who has access to your system and what they do with that access. If your security is too loose, your system and data is exposed. Secure things too tightly and you restrict the agility of your users to perform their tasks in an efficient manner. It’s important to provide users with the level of access they need to do their jobs, while protecting your business from harm.
- Auditing your IBM I security performance.Compliance is an ongoing activity. Auditors want to see proof on an ongoing basis that your system and data are secure. Retaining security data and being able to easily generate reports to demonstrate compliance will save your organization a lot of time and headaches.
- Monitoring your IBM i environment in real time to reduce your risk.Monitoring your environment in real time is the best way to prevent attacks, protect your business from user mistakes, and pinpoint areas to improve. Monitoring can also increase efficiencies by automatically responding to standard messages, freeing up your personnel to work on tasks that can help the business to improve.
The goal of this framework is to create a secure system that’s immune to corruption from bad actors and unintended mistakes. Your security is validated by your auditing and monitoring activities. Your auditing and monitoring activities detect and highlight areas where your security is weak and needs improvement. All three activities work together to create a stronger and more secure IBM i system.
IBM i end to end monitoring and security may seem daunting to some. There are a lot of things to consider, but it doesn’t have to be difficult. SEA offers a suite of tools to help manage your IBM I monitoring and security from end to end, with each product in the suite servicing one of the three critical activities.
It starts with a free IBM i security assessment
It’s important to access the health of your system before you make security changes. That’s why SEA offers a free IBM security assessment to both customers and non-customers. Called the iSecurity Assessment, customers receive one assessment each year as part of their maintenance agreement, while non-customers can contact SEA to receive details on a one-time assessment. Since it’s a yearly offering, a good customer strategy is to conduct an annual security assessment mid-year between the end of your prior audit and the beginning of next year’s audit. Click here to get more details on how to get your free iSecurity Assessment.
Securing your IBM i
Securing activities defend and protect your IBM i by knowing who is accessing your system, how they’re accessing it and what they are doing once access is granted. SEA’s iSecurity suite offers modules that can work together to provide you with the big picture of the state of security across your entire IBM i environment. You can easily secure remote access and exit points, control user authorities, control command usage, prevent viruses, and secure objects.
We consider the following IBM i security areas to be critically important. Here is a description of each security area, what needs to be secured in each area, and the SEA product that helps automate that security.
- Exit Point Monitoring & Intrusion Protection (iSecurity Firewall): Protect and secure access to and from your IBM i by controlling object access at the activity level (read, write, delete, run etc.). Securing native and IFS objects, as well as files, libraries, programs, commands etc.
- Application & Field Level Security (iSecurity AP-Journal): Protect the integrity of your business critical data. Track changes to sensitive business data and send alerts or perform actions if suspicious database activity is suspected, such as order deletion, sales commission changes, or personnel information modification.
- Command Line Access (iSecurity Command): Enforce your security policies by defining accepted command usage at the parameter level. Instead of restricting command line access to users who need it, you can control the parameters they can use and where they can execute the command (for example allow developers to CHGPF in TEST only).
- Emergency User Authority Provisioning & Reporting (iSecurity Authority on Demand): Simplify the process of granting special authorities when needed, and generate reports to document activity performed by users with special authorities.
- Self Service Password Reset (iSecurity Password Reset): Enable self-authentication to improve password security and ease the burden of administering IBM i passwords.
- User and System Value Replication (iSecurity Replication): Provide an easy way to replicate users, passwords and parameters across multiple LPARs. Useful for keeping high availability partitions in sync and setting up security for test, development, or QA partitions. Eases administration and ensures that each environment is in sync.
- Anti-Virus Protection (iSecurity Anti-Virus): Protects the IFS from viruses, Trojan horses and malicious code. Easily scans all files, quarantines and deletes any infected files to prevent your IBM i from being a carrier of viruses that can harm your network.
Auditing your IBM i
SEA’s suite of solutions enables your team to monitor and report on security and system events in real time, providing notification when something happens that needs to be addressed. Here are the specific auditing solutions SEA provides, and how they can help you to audit your environment in real time and provide reports to auditors:
- Audit & Compliance Reporting (iSecurity Audit): Provide real-time monitoring of users and system level activities. Generate 200+ reports for compliance reporting.
- Change Management & Tracking (iSecurity Change Tracker): Automatically monitor and log object changes made to production libraries at both the source and object levels.
- Compliance & Security Scorecards and Ratings (iSecurity Compliance Evaluator): Provides a quick, yet comprehensive view of the level of the IBM i’s compliance with SOX, HIPAA, PCI and other regulations.
- Define Target Object Security Levels (iSecurity Native Object Security): Create a template to easily define target security levels for objects and object types to allow for better control and improved efficiencies.
- Enterprise SIEM integration (iSecurity Syslog): Enables native IBM i syslog integration with other SIEM solutions in real time.
Monitoring your IBM i
One IBM i can generate 100’s of messages daily, if you have multiple systems or LPARs you can have 1,000’s of messages to review. Monitoring is key to ensuring that your system is secure, accessible and meeting the needs of your users. SEA’s absMessage monitoring solution helps increase efficiencies and security by notifying you in real time to any system message. It can centralize and automate resource and message monitoring across multiple LPARs. Notifications and escalation procedures ensure that no critical message is missed. Or even better, define automated responses to standard messages.
Getting started
As we mentioned above, a good way to start reviewing your security is to contact SEA for a free security assessment or for more information on how we can help you with your security issues. We’ll be glad to review your current situation and make recommendations for any changes that might be needed.