What is iSecurity Native Object Security?
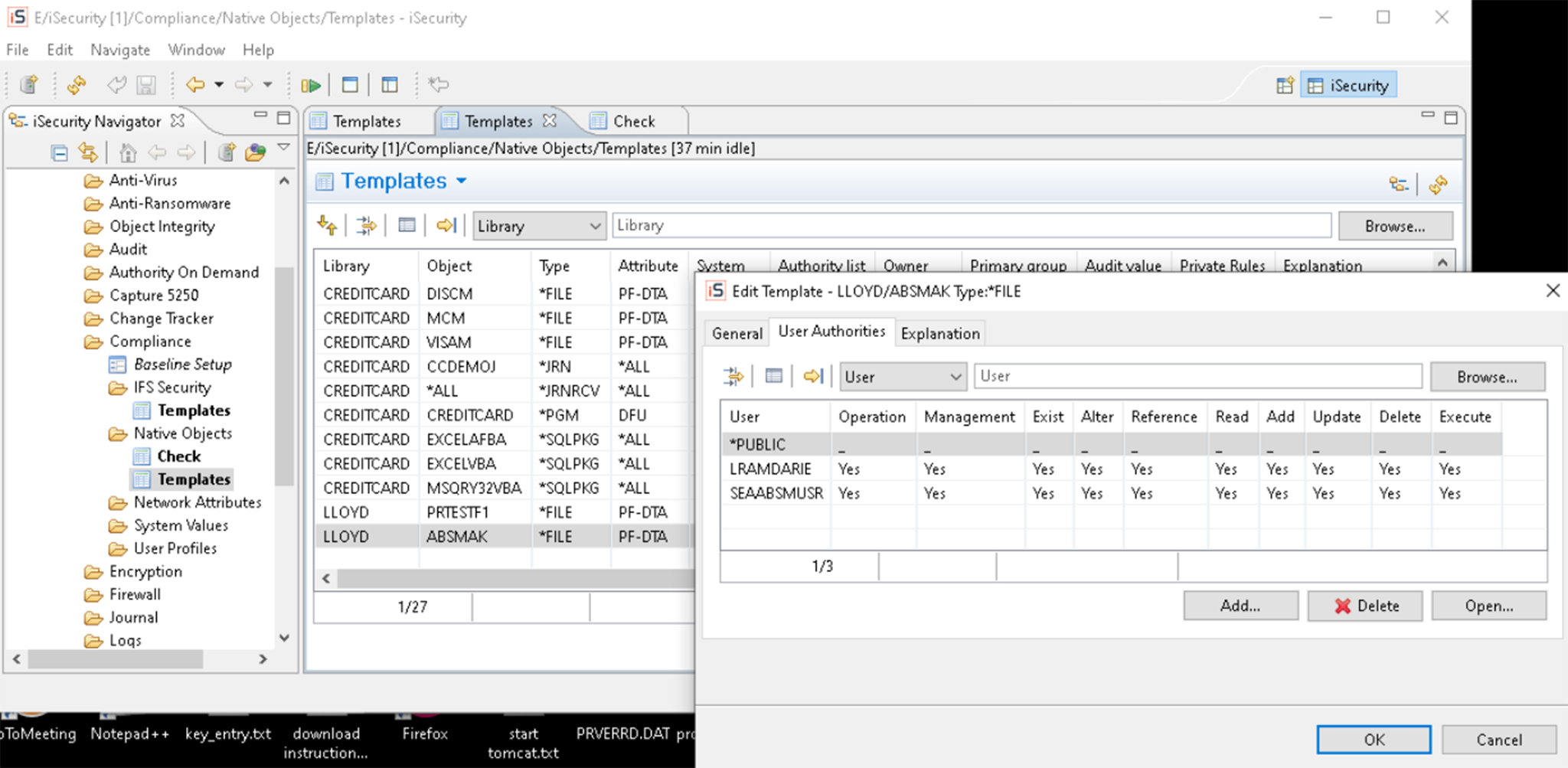
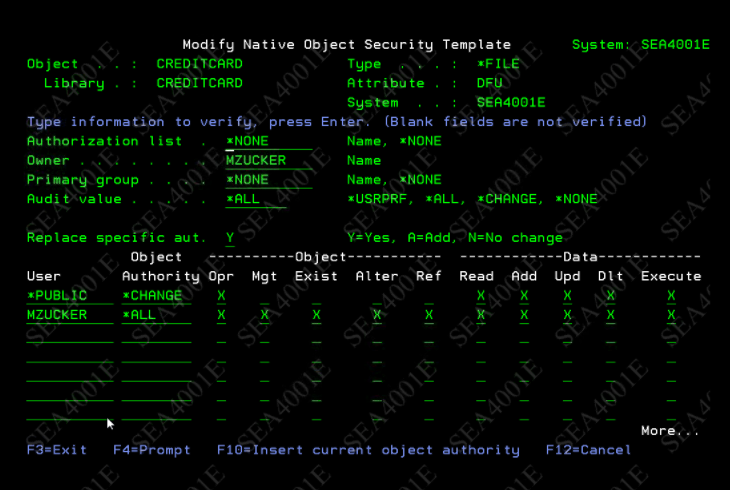
iSecurity Native Object Security’s capabilities enable system administrators to easily define target security levels per IBM i object and object type, and check for inconsistencies between actual and planned object settings.
Native Object Security also enables using generic object names and includes full reporting features.

Easily defines target security levels by object and object type

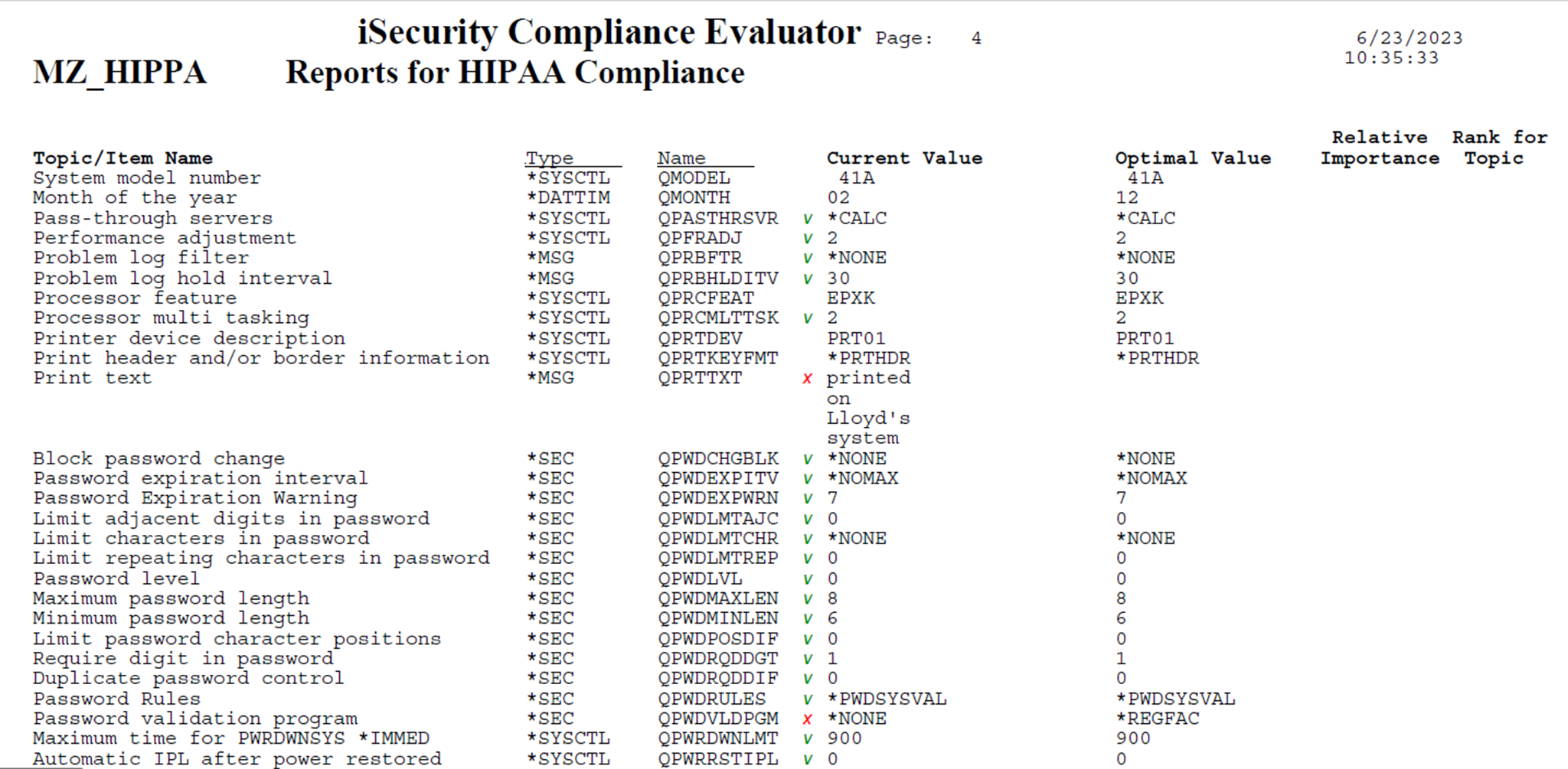
Checks and detects inconsistencies between planned & actual security settings

Provides proof that your data is secure according to planned security settings

Reduces the number of security rules an IBM i admin is required to maintain

Enables multiple object security rules templates for application to different objects
 READ PRODUCT SHEET
READ PRODUCT SHEET