What is iSecurity Replication?
Companies have found it mandatory that system administrators and users alike synchronize user profile definitions, user passwords and profile parameters between different IBM i systems, allowing for exceptions as needed in Production, Test or Development systems.
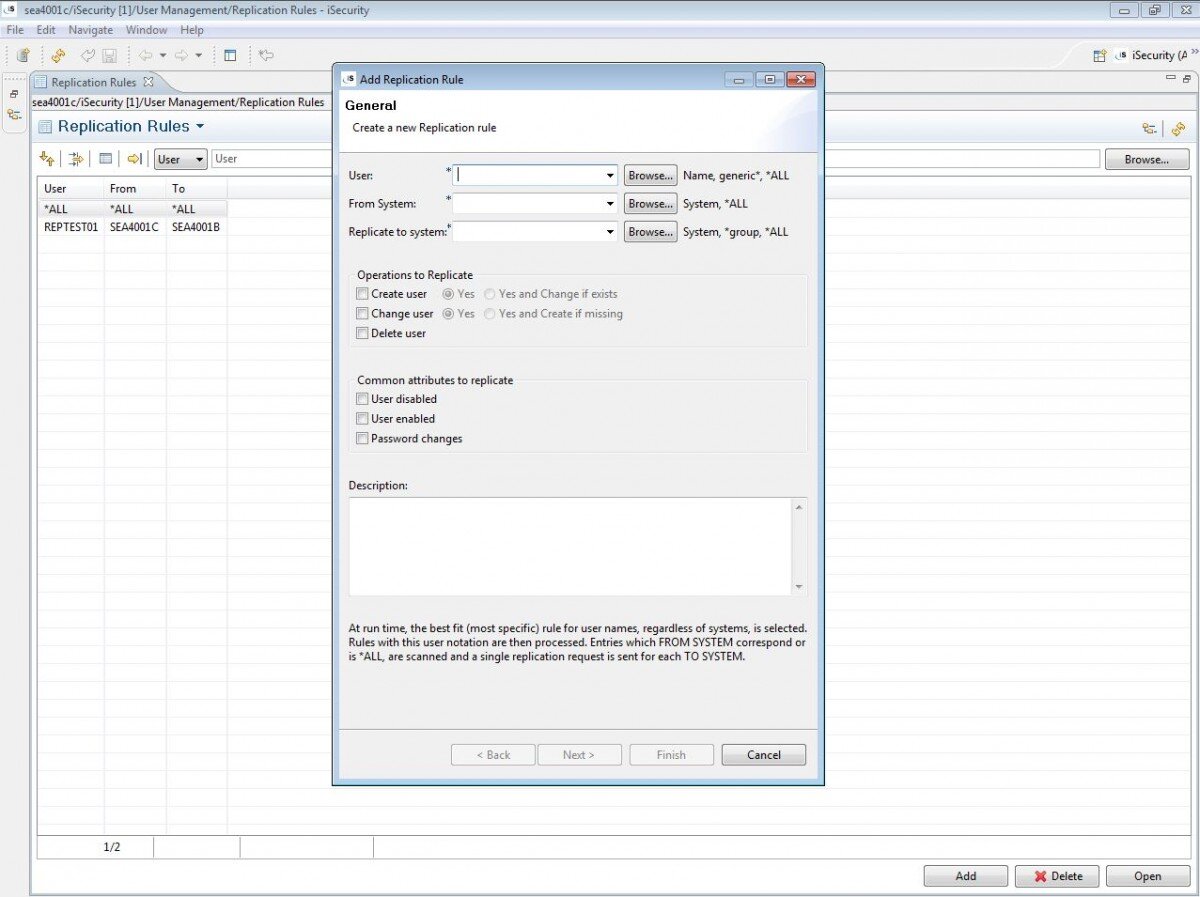
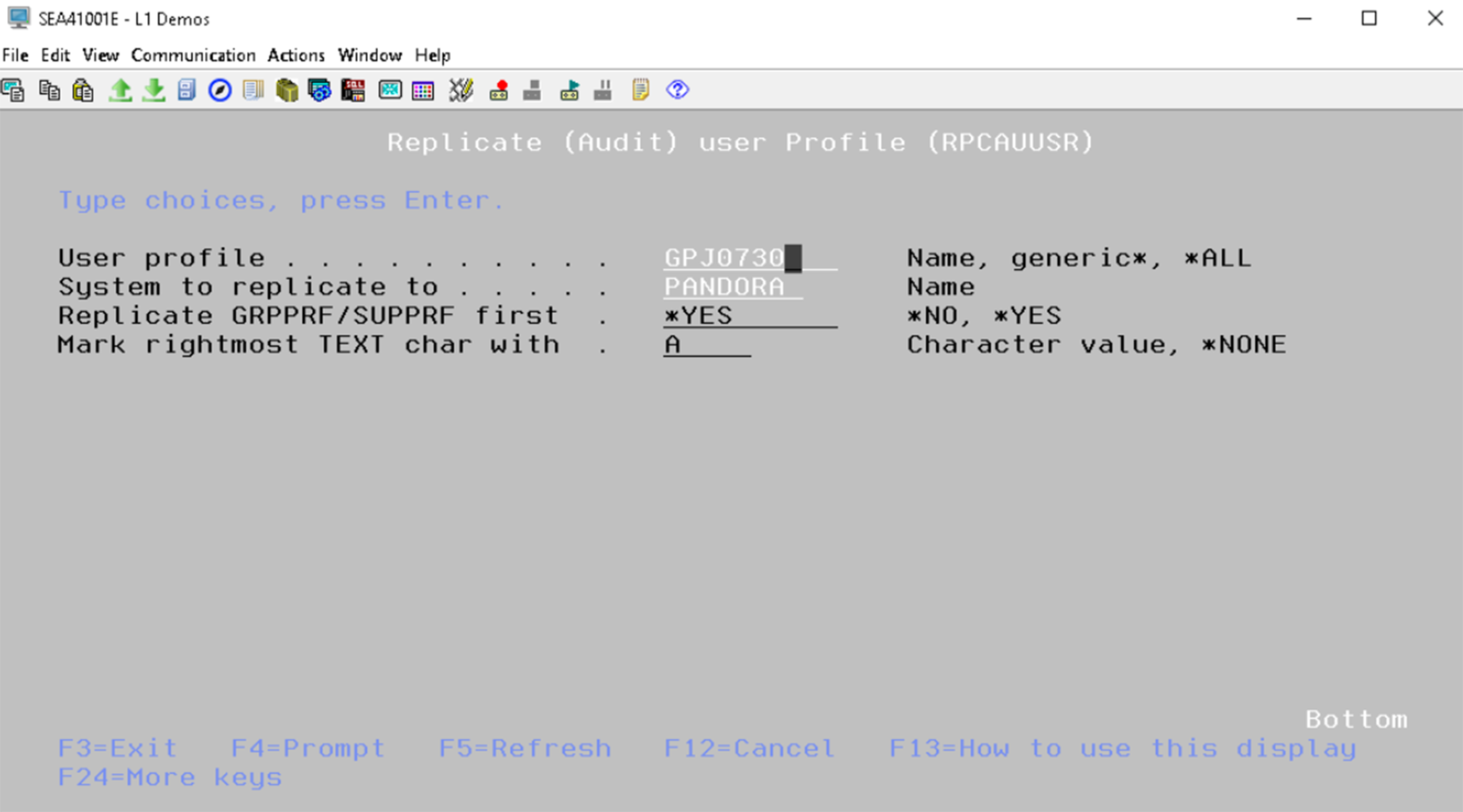
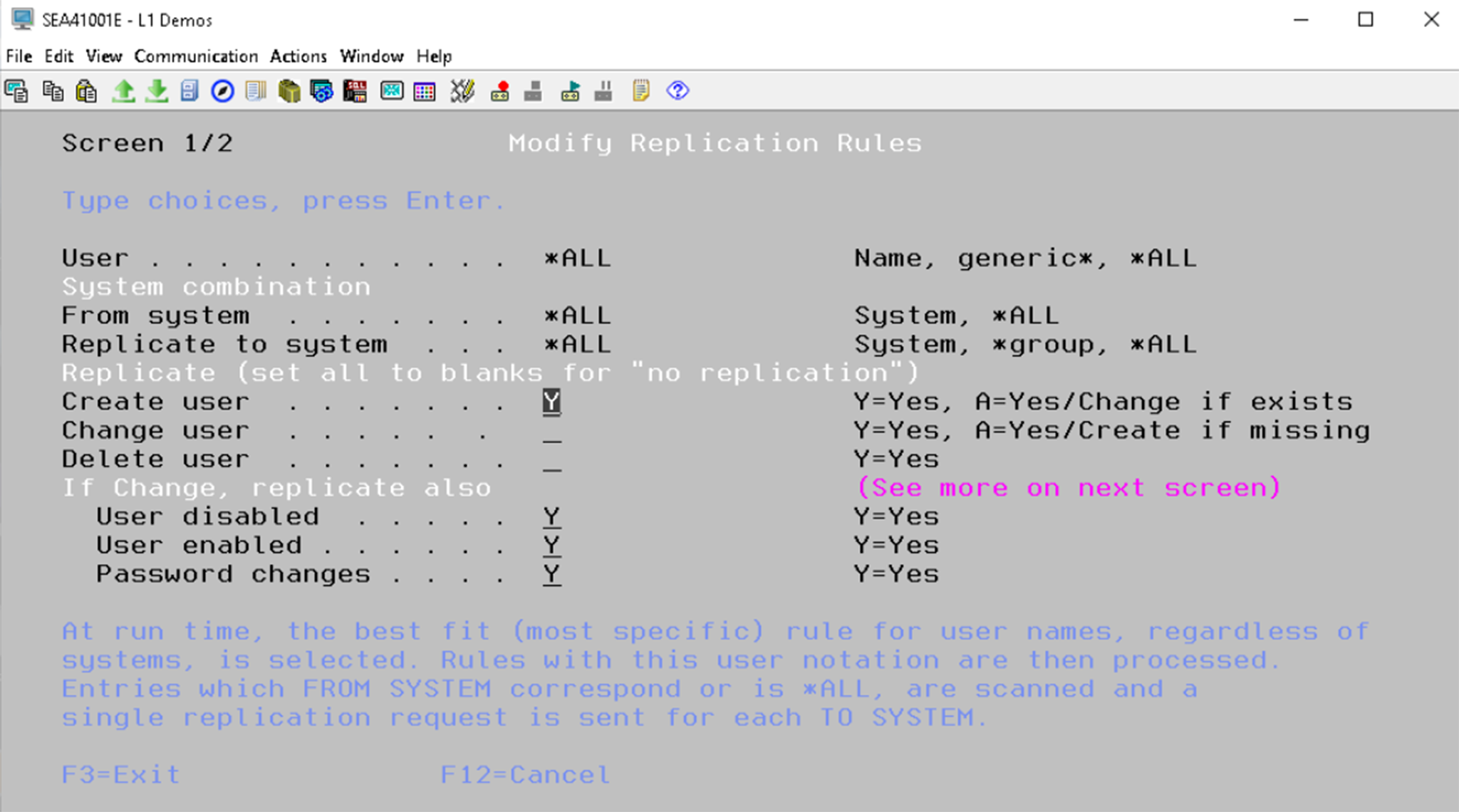
iSecurity Replication provides organizations with flexible user-defined IBM i replication rules for defining user profiles, passwords and parameters.

Synchronization accomplished with minimum system overhead and minimum administrator activity

Replication can be initiated from any IBM i & does not require any special commands

Allows organizations to set user profile definitions to optimal values or set site-defined baseline values

Allows administrators to revive and modify parameters for deleted users

Bulk updates of user profiles save time in changing global parameters
 READ PRODUCT SHEET
READ PRODUCT SHEET