iSecurity Compliance Evaluator
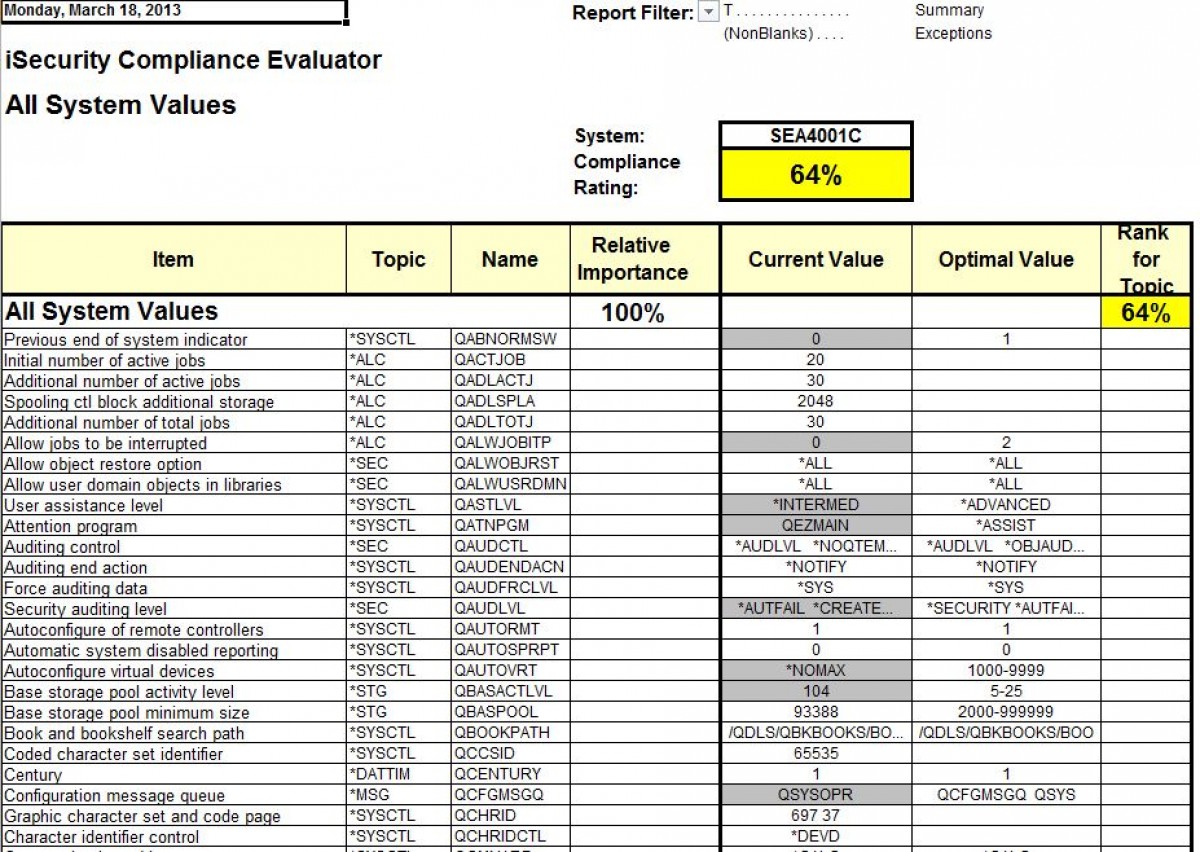
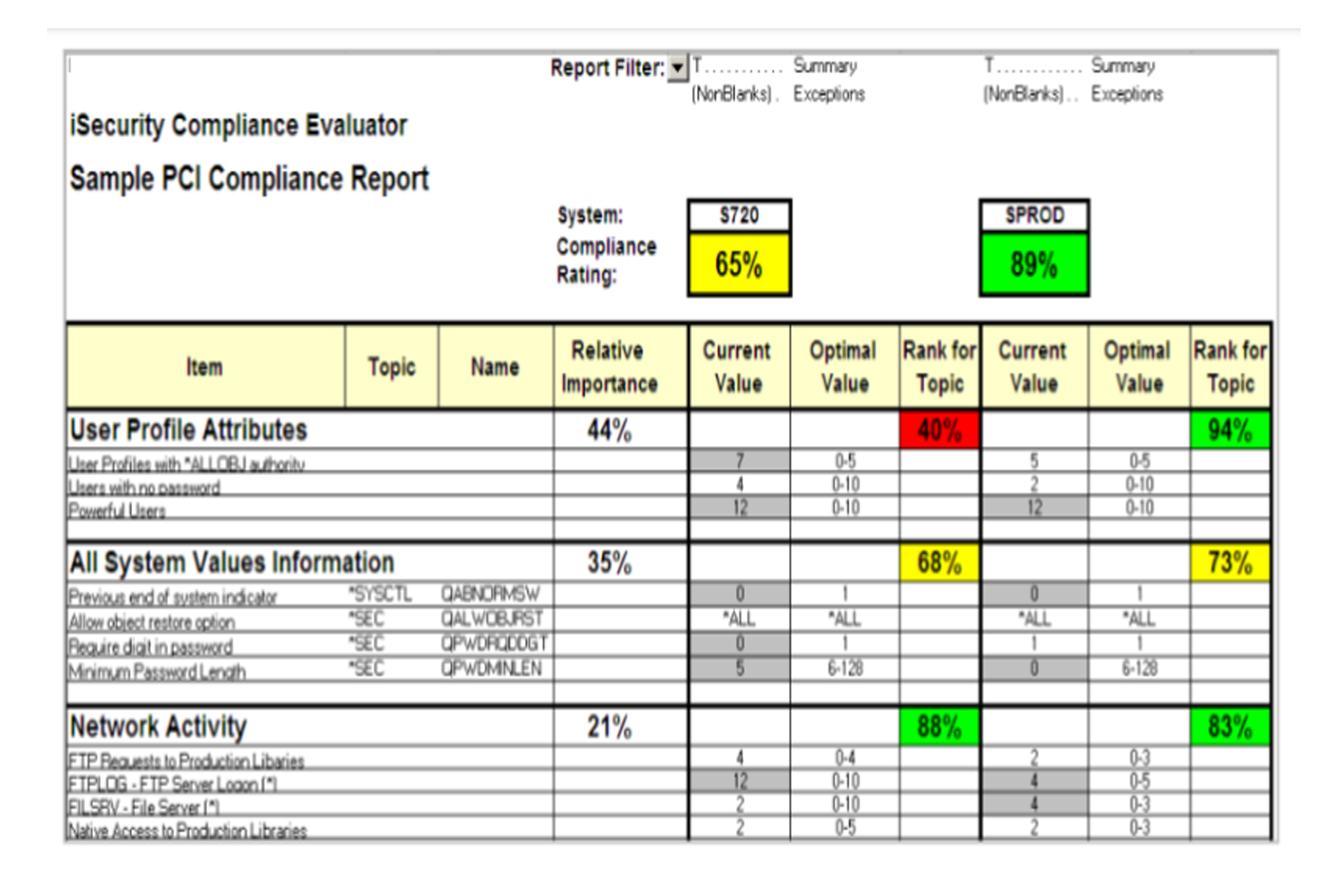
iSecurity Compliance Evaluator provides managers, auditors and systems administrators a quick, yet comprehensive overview of their IBM i's level of compliance with PCI, SOX, HIPAA and other government, industry or enterprise-related regulations.
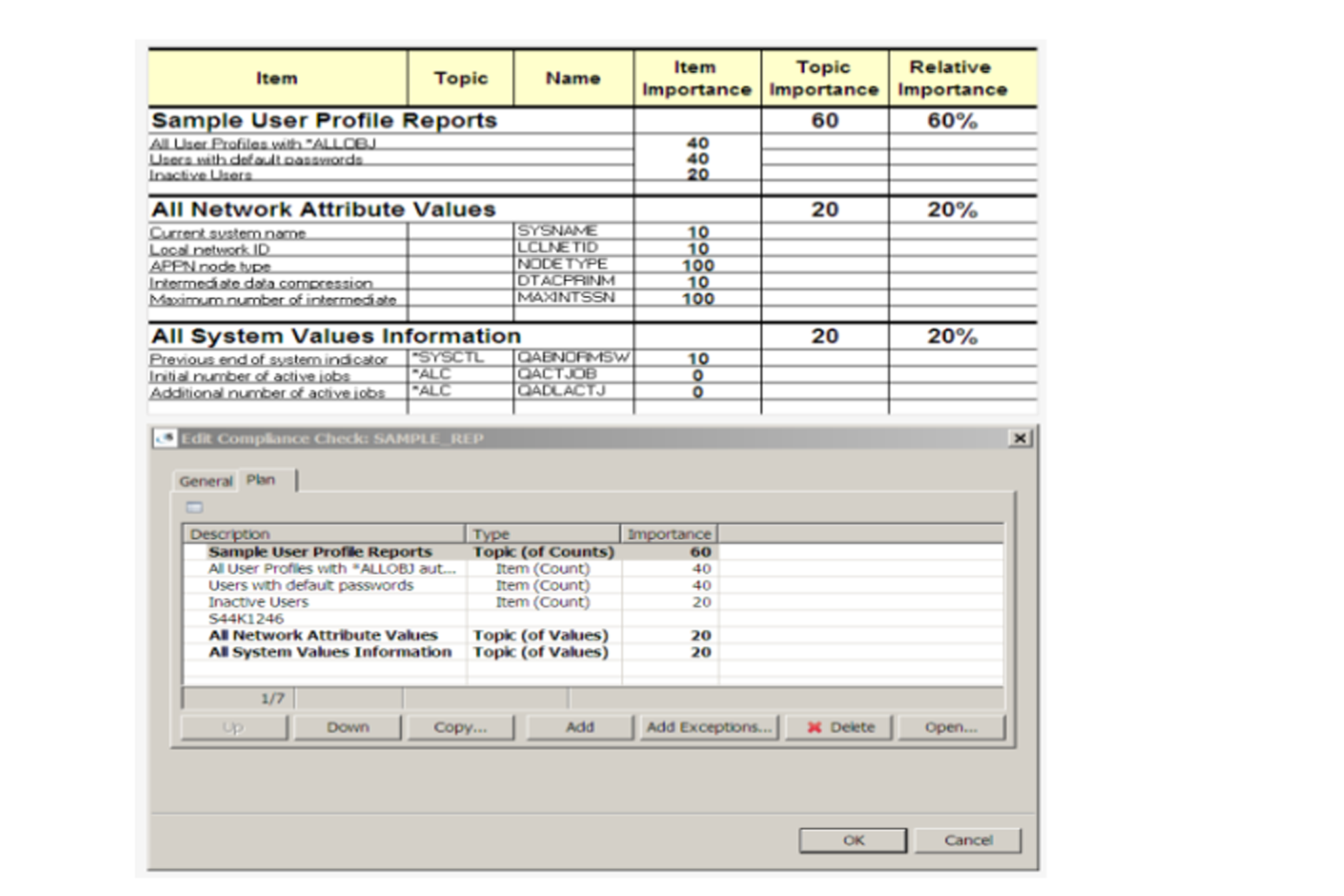
Reports include useful operational information derived from QAUDJRN and network activity. Any type of information can be added. The result is a colorful and user-friendly view of compliance level.
This solution provides a network-wide compliance assessment with an overall compliance score and specific ratings for topics for all your IBM i systems.

PCI, SOX, HIPAA and other compliance checks

Results can be scheduled and emailed directly from your IBM i systems

Scores and a Scoring System that adheres to your Administrator's defined measurements

Reports unexpected changes on a broad range of customizable activities on IBM i servers

User-friendly GUI interface
 READ PRODUCT SHEET
READ PRODUCT SHEET